European MPs caution against the impending quantum computing revolution, which promises to undermine current encryption safeguards. Experts echo this urgency, warning that existing security measures for sensitive data are on borrowed time. With quantum computers inching closer to breaking mathematical keys and countries like China showing an insatiable appetite for data, the race is on to develop quantum-safe products.
The specter of quantum computing, with its potential to crack the cryptographic keys that protect everything from personal emails to state secrets, casts a long shadow over the digital world. European MPs, led by Dutch MP Bart Groothuis, have sounded a clarion call in a letter they sent to the European Commission: the cryptography underpinning our computer security systems is a ticking time bomb. This alarm is not unfounded. With quantum computing’s ability to process complex calculations at breakneck speeds, the security protocols we rely on today could be rendered obsolete almost overnight.
Why this is important
Quantum computing is set to disrupt our computing possibilities, fundamentally disrupting computation. However, quantum computing doesn’t come without its own risks, as it has the potential to undermine current data encryption safeguards.
A quantum leap for computing, a potential fall for security
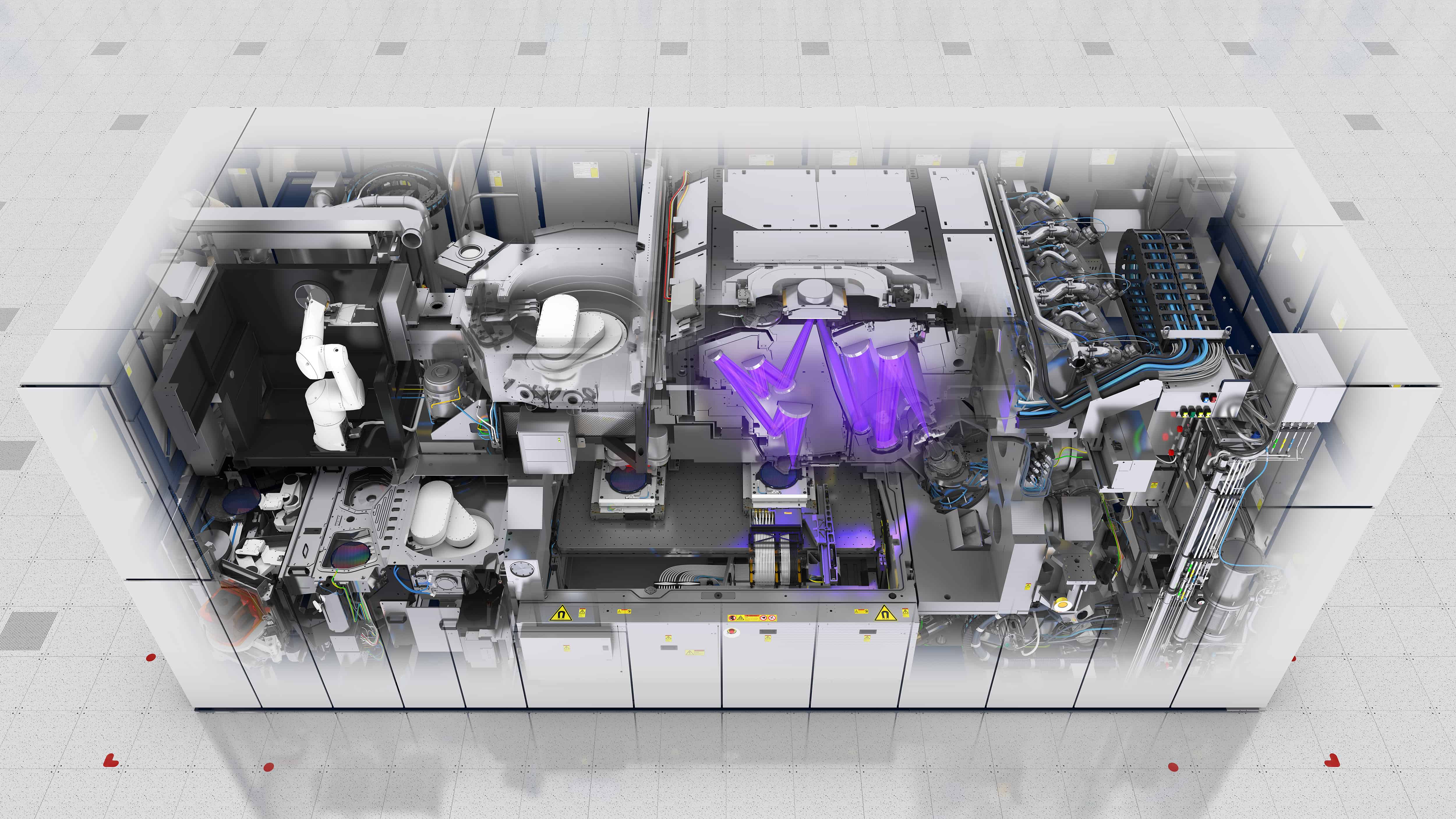
Quantum computers differ radically from today’s computers. They utilize qubits, which, through superposition, can represent both one and zero simultaneously. This fundamental change in computation allows quantum computers to solve specific problems—like factoring large numbers, the basis of much of our encryption—exponentially faster than classical computers. When a quantum computer with enough stable qubits comes online, it could break the RSA-2048 encryption, a standard for securing web traffic, within a day. The more optimistic estimates give this scenario an 11 percent chance of occurring within the next five years, a figure that rises to a worrying 33 percent over the next fifteen years.
The MEPs’ letter: a call to action
In a letter that underscores the gravity of the situation, MEPs laid out the stark timeline we face: switching to a new cryptographic standard could take over a decade, paralleling past transitions like the adoption of the SHA2 hashing algorithm and the AES symmetrical algorithm. The letter implores major organizations to begin preparations immediately for a complete post-quantum cryptography (PQC) transition. The National Institute of Standards and Technology (NIST) in the United States has already identified algorithms for this purpose, with choices like CRYSTALS-Kyber for public key encryption and CRYSTALS-Dilithium, FALCON, and SPHINCS+ for digital signatures.
The MEPs’ letter recommends that the European Commission, alongside bodies such as the European Union Agency for Cybersecurity (ENISA), the European Data Protection Supervisor (EDPS), and the European Data Protection Board (EDPB), offer clear guidance on what constitutes “appropriate” security measures in anticipation of quantum capabilities. The MEPs suggest this should include inventorying current algorithms, assessing new cryptographic libraries, deploying hybrid encryption systems, and beginning a phased deployment of NIST-approved standards.
Preparing for the quantum future
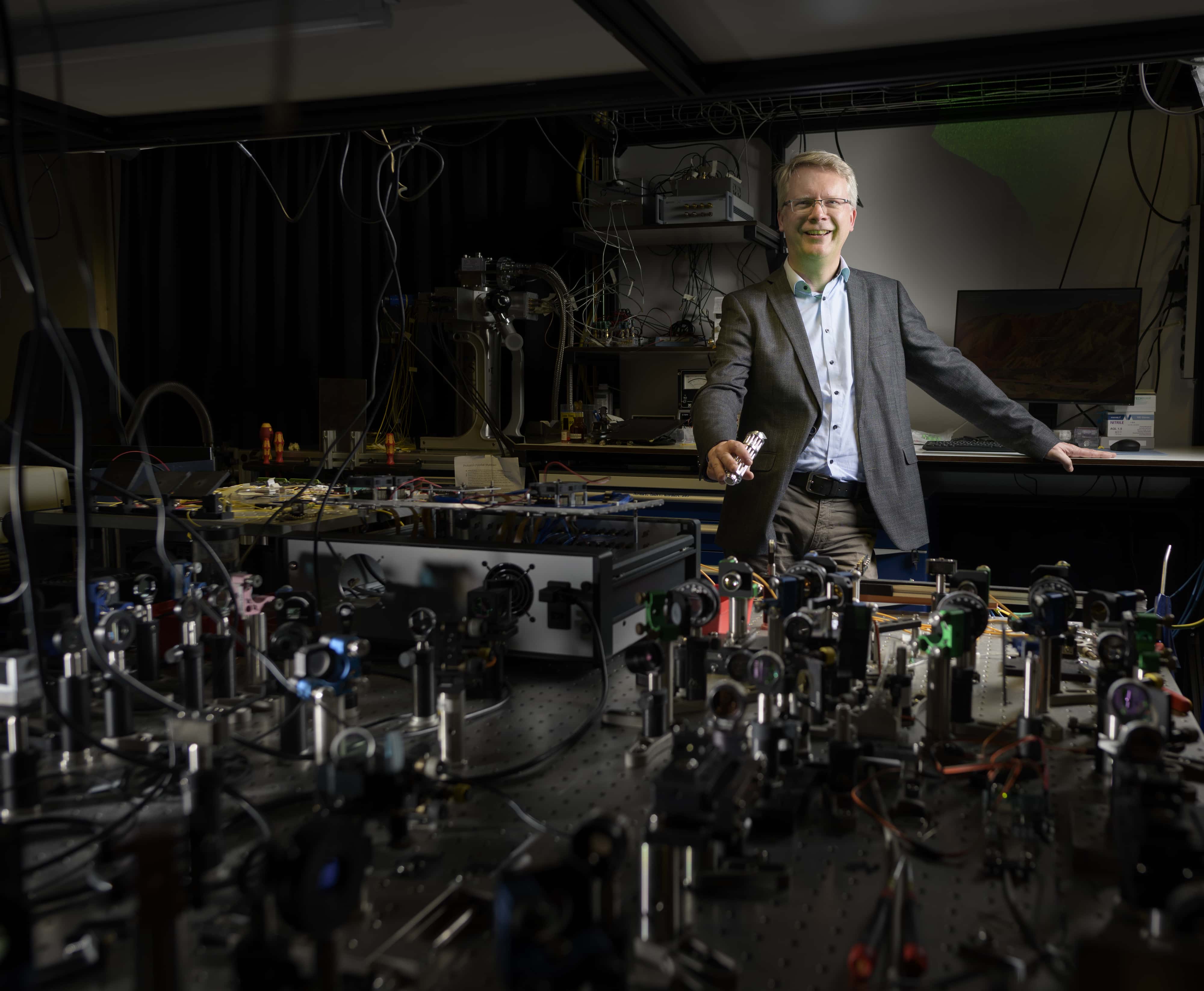
Professor Pepijn Pinkse, a quantum technology expert, previouslypep warned about the risks of quantum computing security. Pinkse’s work underscores the fundamental shift required in our approach to cryptography. Most current cryptography relies on the difficulty of reversing the multiplication of large prime numbers. Quantum computing, particularly using the Shor algorithm, could make that reversal trivial. Pinkse and other experts indicate that “Q-Day”—when current cryptographic security systems capitulate to quantum computing—is less than a decade away.
Indeed, the quest to build a quantum computer is not just a scientific challenge—it’s a geopolitical one. The past decade has seen a quadrupling in the number of companies actively developing quantum computing hardware. Investment in the field has been substantial, with multiple funding rounds in the quantum computing market exceeding $100 million between 2022 and 2024. National laboratories and supercomputing centres, often driven by government interest, are pouring resources into early-stage machines. The implications for economic and national security are profound.
It remains to be seen how the European Union’s institutions and member states will react to the MEPs’ letter. Will they heed the warnings and start the necessary transitions to safeguard against the quantum threat? The clock is ticking, and as the MEPs’ letter makes clear, the time to act is now—before the quantum revolution undoes the digital security we’ve come to rely on.