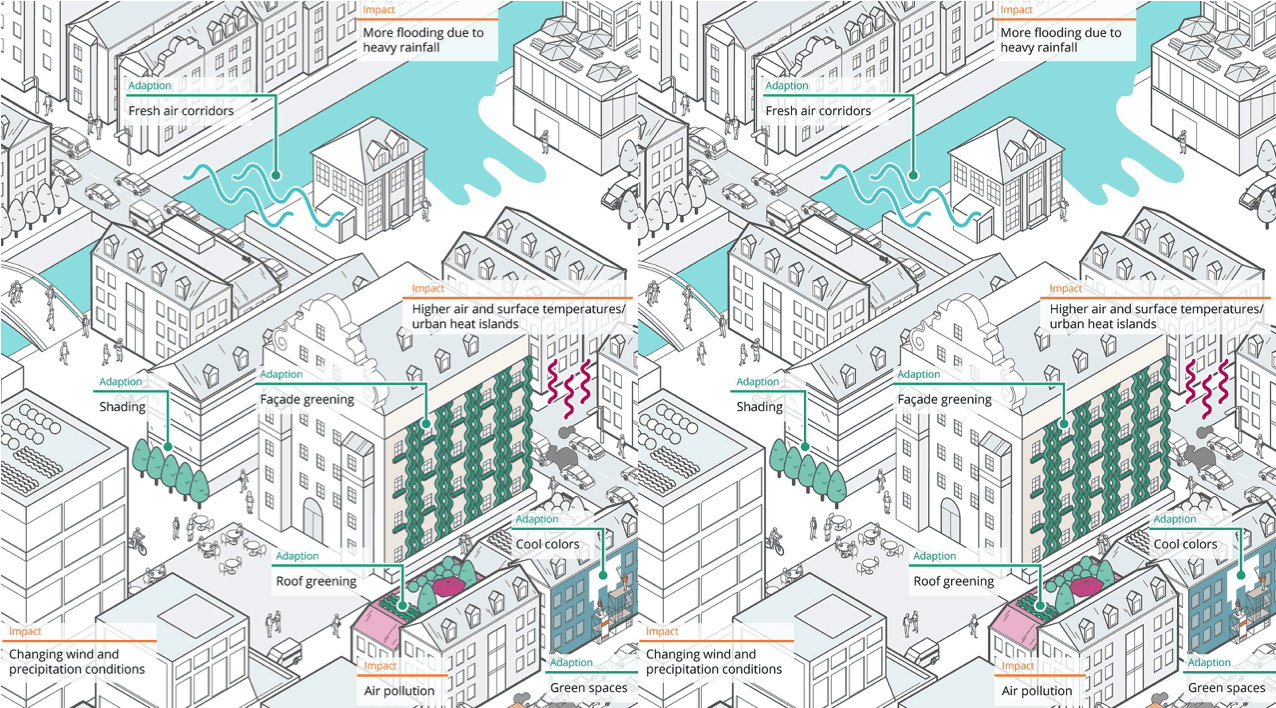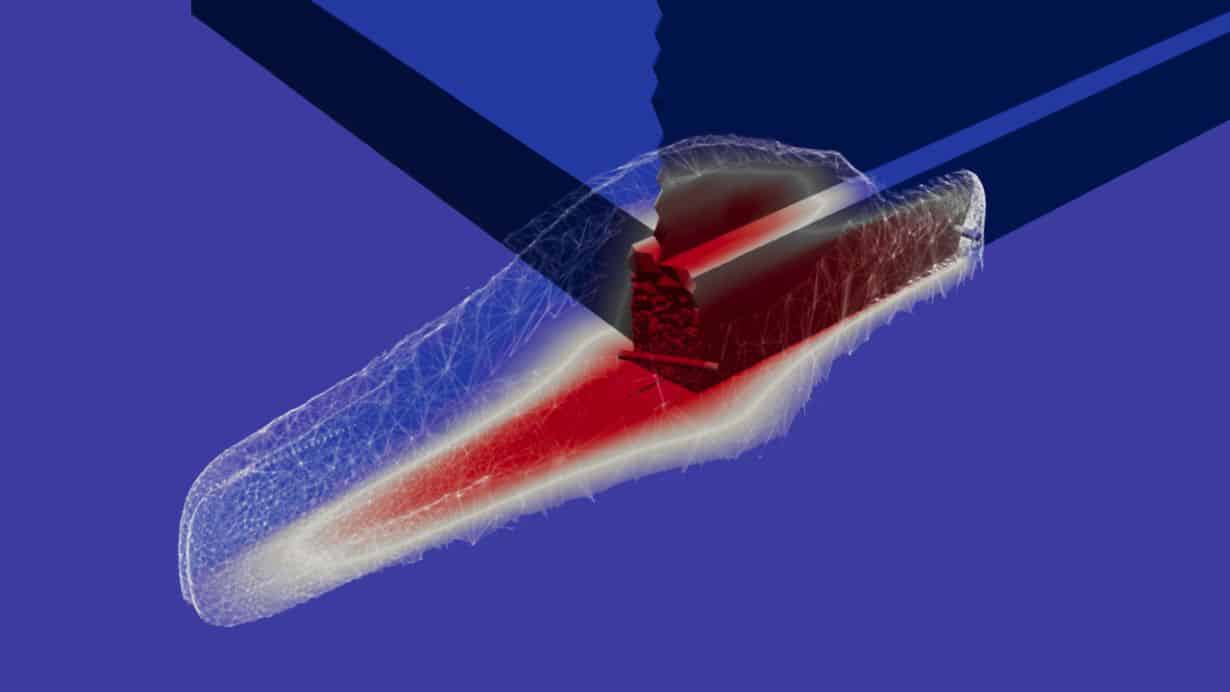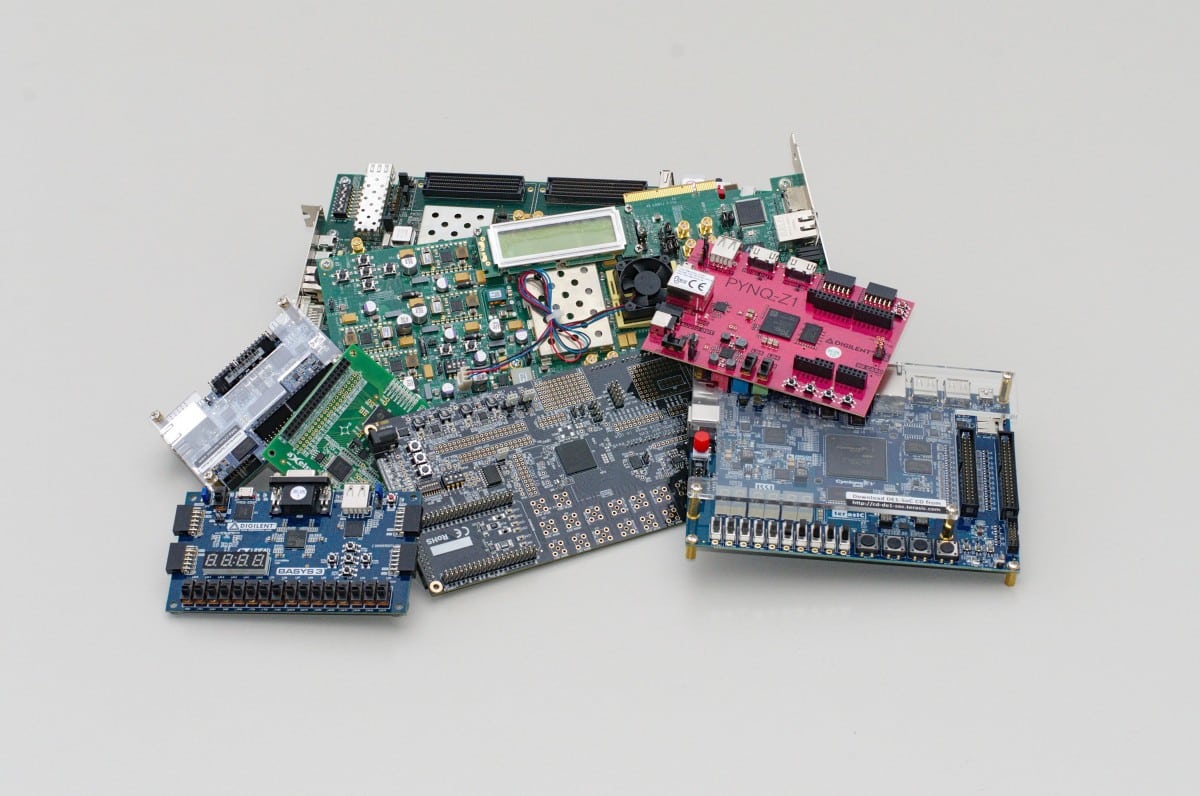
Actually, they’re pretty handy, the FPGAs. The abbreviation stands for Field Programmable Gate Arrays. Their advantage is: these programmable gate arrays are much more flexible than ordinary specialized computer chips. And so far, they have even been considered particularly secure. But now researchers at the Karlsruhe Institute of Technology (KIT) have found potential gateways for cyber criminals in these electronic components. Especially if the FPGAs are used by several users. And this often happens. Because they are used in large data centers, which in turn are used for cloud services of large tech companies and the Internet of Things.
Comparison: Lego Bricks Instead of Modelling Clay
While conventional chips can usually only perform special, constant tasks, FPGAs are able to assume almost any function of any other chip. Therefore, they are often used in the development of new devices or systems.
FPGAs, for example, are used in the first product batch of new devices because, in contrast to a special chip, whose expensive development is only worthwhile for very large quantities, they can be modified later”, explains Dennis Gnad from the Institute of Computer Engineering (ITEC) at KIT.
The computer scientist explains that this could be imagined as building a sculpture from reusable Lego bricks instead of binding modelling clay.
Low Power Consumption and Arbitrary Distribution
FPGAs are used, for example, for smartphones, networks, the Internet, medical technology, automotive electronics and aerospace. A further advantage, namely their low power consumption, also makes them attractive for use in the server farms of cloud services. Especially since they can be distributed as desired.
“This way, one customer can use the upper half of the FPGA, another the lower half”, says Jonas Krautter, also from ITEC, describing the application of the programmable chips. In cloud services, for example, the chips deal with tasks in the fields of databases, AI applications such as machine learning or financial applications.
And this is where the problem lies:
The use of a chip with FPGA by multiple users at the same time is a gateway for malicious attacks”, warns Gnad.
The versatility of FPGAs would give tricky hackers the opportunity to carry out so-called side-channel attacks. The attackers use the chip’s energy consumption to extract information with which they can crack its encryption. This would enable one customer of the cloud service to spy on another by means of the internal chip measurements. It would also be possible for hackers not only to spy out treacherous fluctuations in power consumption, but also to generate them themselves.
Solution: Restriction of Access
“This can falsify the calculations of other customers or even crash the entire chip, which could result in data loss”, explains Krautter. Similar dangers exist with other chips, Gnad continues. Such as those frequently used in Internet of Things applications such as intelligent heating controls or lighting. And when you consider the areas in which these services are now used for business and private purposes, it’s definitely time to act.
The solution proposed by Gnad und Krautter is to restrict users’ direct access to the FPGAs.
The difficulty lies in filtering out malicious users without restricting benevolent users too much”, Gnad notes.
The study was recently published in the specialist journal ICAR.