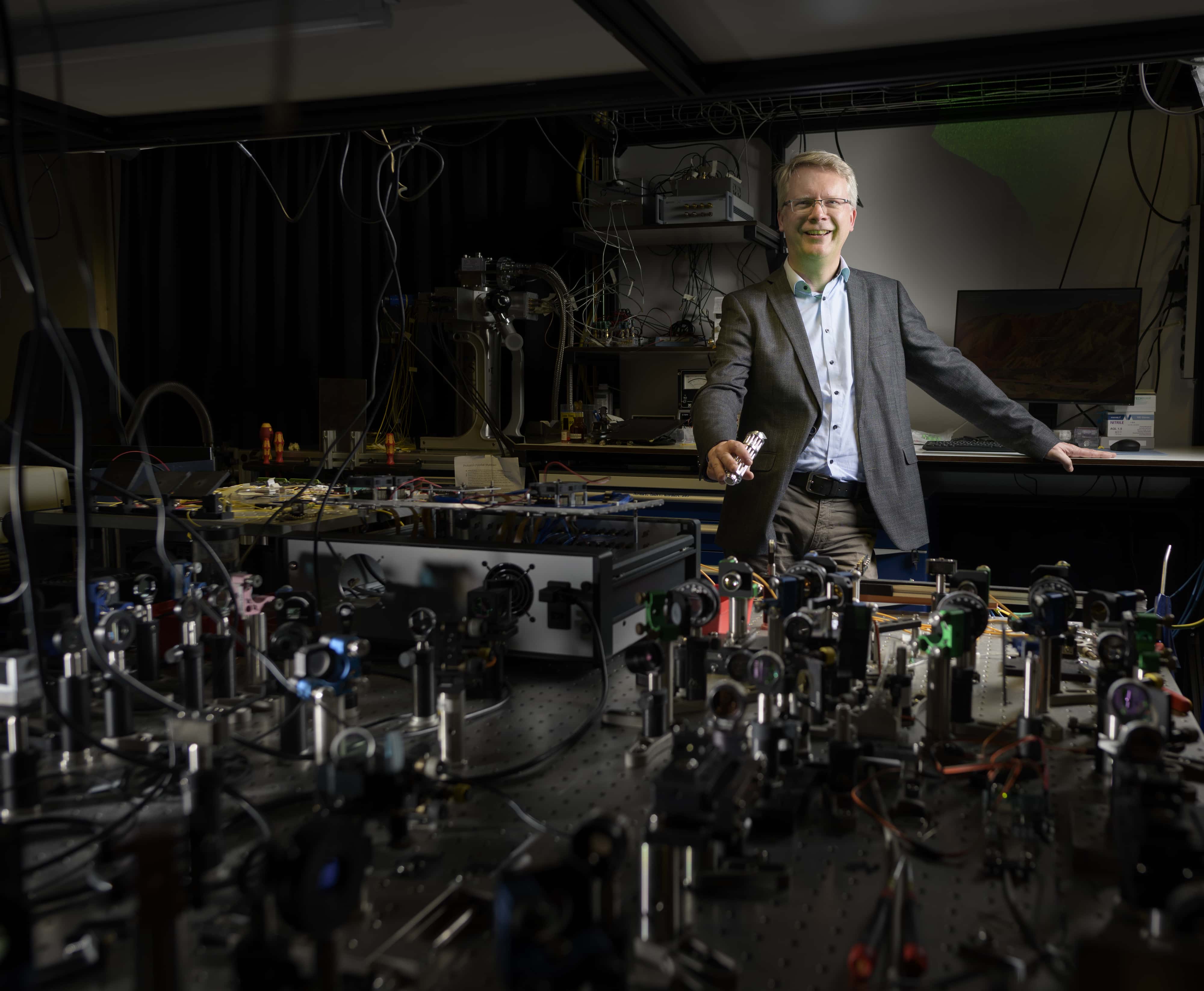
Intel’s Thunderbolt connection is poorly secured. Master student Björn Ruytenberg of the University of Technology in Eindhoven, Netherlands, has discovered seven security holes in the systems running on Windows or Linux. Intel has been informed of the problem and the company has already taken measures. However, these are only available to a limited number of users.
Millions of PCs and laptops are still at risk of being hacked via the Thunderbolt connection. Björn Ruytenberg and his supervisors from the Faculty of Mathematics and Computer Science advise all users of Thunderbolt to turn off the functionality.
Almost every computer is equipped with Thunderbolt, a computer port for fast data transfer between a PC or laptop and other devices, such as an external hard drive. The technology can be found in hundreds of millions of devices worldwide. Almost every new laptop and desktop computer produced since 2011 is equipped with Thunderbolt. The port can be recognized by the small symbol of a lightning bolt.
Intel claims that access via Thunderbolt is protected by cryptography to prevent hackers from gaining unauthorized entry to a computer. “But,” says Ruytenberg, “to my surprise, I haven’t been able to discover anything that actually resembles modern cryptography. The little that was there I could easily crack or bypass,” he says in an interview that appeared today on the Eindhoven University of Technology website.
Nine realistic hacking scenarios
Ruytenberg found seven security holes in Thunderbolt’s design and developed nine realistic scenarios under the name Thunderspy to see how someone with malicious intent could exploit them. Thunderspy works independently of the victim. There is no need for him to accidentally connect a malicious device or install malware. All the attacker needs are five minutes of undisturbed access to the computer, a screwdriver, and some easily portable hardware. Once inside, he can read and copy all data, even if the hard drive is encrypted or the computer is locked or in sleep mode. The attack leaves no trace, so the victim doesn’t know he’s been hacked.

No update for devices provided until 2019
The Eindhoven University of Technology research team contacted Intel in February to share its findings with them. The company confirmed the vulnerabilities. However, Intel’s only solution so far is Kernel DMA Protection. It offers protection against some of the vulnerabilities in Thunderbolt, but has only been available since 2019 and only on a limited number of PCs and laptops. In addition, Kernel requires DMA hardware support so it cannot be retrofitted to older systems. Therefore, any Thunderbolt-enabled system produced before 2019 and the majority of systems produced after that date will not receive a patch or update.
Full disabling of Thunderbolt
Ruytenberg advises all users of PC’s and laptops to download Spycheck via the website Thunderspy. This is a tool specially developed by him that checks whether a device is vulnerable. Spycheck leads users to recommendations on how to protect their systems. One of the solutions is to completely disable Thunderbolt in the BIOS settings. It is also wise not to leave any system with Thunderbolt unguarded – not even for five minutes. Ruytenberg’s findings will be presented at BlackHat USA2020, a major information security conference to be held in the United States in August.